Microsoft Warns of Monster Bug, In a Week of Them--2nd Update
16 May 2019 - 3:36AM
Dow Jones News
By Robert McMillan
Microsoft Corp. took the unusual step of warning that a computer
bug it has now patched could be used by a cyber weapon similar to
the WannaCry worm, which spread across the globe two years ago.
The bug is one of several high-profile computer-security issues
to emerge this week, though the impact isn't yet clear.
Microsoft said that it hasn't seen anyone take advantage of the
flaw, which affects older versions of its Windows operating system,
but that it believes it is "highly likely" the flaw will wind up
being exploited by malicious software, now that it has been
publicly disclosed.
Any "future malware that exploits this vulnerability could
propagate from vulnerable computer to vulnerable computer in a
similar way as the WannaCry malware spread across the globe,"
Microsoft said Tuesday in a blog post.
The flaw affects Windows 7 and Windows Server 2008. It also
affects Windows 2003 and Windows XP -- older versions of Windows
that Microsoft doesn't typically patch. But, in a sign of the
severity of the bug, Microsoft released XP and Windows 2003 patches
as well.
"This is certainly one to take seriously," said Chris Coulter,
vice president of technology with BlackBerry Ltd.'s Cylance
security group.
Users of Windows 10 and Windows 8 aren't affected by the flaw,
Microsoft said.
Microsoft said the best way for companies to protect themselves
against the vulnerability is to upgrade to newer versions of its
software, which are harder to hack and include better tools for
automatic updating of patches.
In the case of the WannaCry attack, Microsoft had issued a patch
months before the ransomware began spreading globally. But some
companies hadn't installed the fix, either out of lax security
practices or concerns about disrupting their day-to-day
operations.
Any time a company deploys new code like a patch, the
installation could fail or run into other glitches, or the software
could end up incompatible with a company's existing programs --
potentially costly hiccups. All those issues leave companies
vulnerable despite an available fix.
Plenty of companies can install software updates with little
disruption. But large institutions can take months to test and
deploy patches to avoid business disruptions. That patching process
can be drawn out at hospitals, power plants and other critical
institutions that can't afford to go offline for hours at a time,
cybersecurity specialists say.
WannaCry spread quickly, and infected more than 200,000 systems
world-wide with ransomware -- software that rendered computer
systems unusable and demanded a digital ransom. It affected systems
at England's National Health Service, FedEx Corp. and Nissan Motor
Co.
The 2017 worm could have been more devastating, but it was
stopped when a security researcher activated a "kill switch"
feature that prevented the worm from spreading.
Microsoft's bug came a day after Facebook Inc. patched its
WhatsApp encrypted-messaging application following the company's
disclosure it had been used in a novel form of attack: Hackers had
found a way to install spyware on mobile phones by using a bug in
the voice-calling feature of WhatsApp.
The attack was used in hacking tools created by an Israeli
cybersecurity firm called NSO Group Technologies Ltd, according to
people familiar with the WhatsApp bug investigation.
NSO Group sells its hacking and spyware tools to law enforcement
and government agencies. A spokeswoman for the company declined to
say whether NSO Group had created attack code leveraging the bug,
but said the company doesn't identify targets or operate its
technology against them.
Three years ago, NSO Group's software was linked to an attack
against Apple's iPhone.
That flaw was particularly interesting because WhatsApp is often
used by security-conscious people looking to take advantage of its
end-to-end encryption capability, which prevents others from
snooping on messages as they are sent, Mr. Coulter said. "Myself
and millions of others inadvertently put all that at risk by
blindly trusting the app," he said.
On Tuesday, Intel disclosed issues in its microprocessors that
could allow hackers to gain unauthorized access to data stored in a
computer's memory. The new bugs are similar to last year's Spectre
and Meltdown flaws, but are hard to exploit and unlikely to cause
the kind of widespread havoc of a computer worm, security
researchers said.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
May 15, 2019 13:21 ET (17:21 GMT)
Copyright (c) 2019 Dow Jones & Company, Inc.
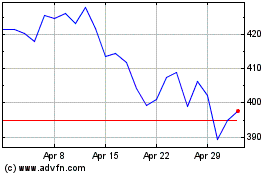
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Mar 2024 to Apr 2024
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Apr 2023 to Apr 2024
