By Robert McMillan
The woman who allegedly pulled off one of the largest-ever
bank-data heists appeared to have exploited a vulnerability in the
cloud that security experts have warned about for years.
Paige A. Thompson, a former employee at Amazon.com Inc.'s
cloud-computing unit who was arrested Monday, is accused of
carrying out the massive theft of 106 million Capital One Financial
Corp. records.
Capital One has said "a specific configuration vulnerability"
led to the data loss.
Ms. Thompson was allegedly able to find an opening in Capital
One's systems and exploit a weakness in some misconfigured
networks, according to a Wall Street Journal analysis of hundreds
of Ms. Thompson's online messages and interviews with people
familiar with the investigation. Security professionals for years
have warned about that gap, which the messages and interviews
suggest she used to trick a system in the cloud to uncover the
sensitive credentials she needed to access the vast number of
customer records.
Ms. Thompson, in online messages in accounts that prosecutors
have said were hers, claimed to have also applied those techniques
to access a trove of online data from other organizations. The
messages were posted in online forums.
Ms. Thompson's lawyer didn't respond to requests for comment.
She remains in detention and is scheduled for a bail hearing on
Aug. 15.
At the heart of the digital break-in was Ms. Thompson's apparent
ability to tap into a central piece of Amazon's cloud technology
known as its metadata service. It holds the credentials and other
data needed to manage servers in the cloud. The credentials
effectively are the computer world's equivalent to the keys to a
bank vault.
In the first step of her alleged hack that began in March,
according to her online postings, Ms. Thompson ran a scan of the
internet to find vulnerable computers that could give her access to
a company's internal networks. Effectively, she knocked on many
front doors to hunt for ones that were unlocked.
In the case of Capital One, she found an unsecured computer that
provided the portal between the company's secured network and the
public internet, according to people familiar with the
investigation. The door was open.
Through that opening, she was able to send a request to the
Amazon cloud metadata tool kit for the credentials needed to search
Capital One's cloud-stored data, the people said.
"Dude so many people are doing it wrong," Ms. Thompson said in a
June 27 online message, referring to how some companies were
incorrectly configuring their servers.
With the credentials retrieved from the metadata tool kit, she
was able to find Capital One data and then easily download the
information, the people familiar with the investigation said. All,
apparently, without triggering any alerts.
Amazon said in a statement that none of its services --
including the metadata service -- were the underlying cause of the
break-in and that it offers monitoring tools designed to detect
this type of incident.
It is unclear why none of these alerting tools appear to have
triggered alarm bells at Capital One.
A Federal Bureau of Investigation affidavit said a Capital One
error enabled the breach. Capital One said it now has fixed the
configuration problem.
Some security experts say that Amazon should do more to alert
its customers about these configuration errors. Others say, given
that cloud security is a shared responsibility, corporate customers
have to do their part.
Amazon has said it has several tools to help mitigate
configuration slip-ups.
Prosecutors have said that Ms. Thompson began her hacking on
March 12, but Capital One didn't learn of it until it was tipped
off by an outside researcher 127 days later.
Security professionals have known about one of these
misconfiguration problems -- the ability to pilfer credentials from
the metadata service -- since at least 2014, said Scott Piper, who
advises companies on their Amazon cloud security. Amazon has
considered it the customer's responsibility to eradicate them, he
said, and some customers have failed to do so.
Brennon Thomas, a security researcher, conducted an internet
scan in February and found more than 800 Amazon accounts that
allowed similar access to the metadata service. Amazon's
cloud-computing service boasts more than one million users.
Mr. Thomas said the problem of misconfigured servers enabling
outsiders to access sensitive metadata isn't limited to Amazon Web
Services, or AWS. His test also found problems with systems running
on Microsoft Corp.'s cloud. Microsoft didn't respond to requests
for comment.
That Capital One was a victim has surprised some researchers.
The bank performed extensive due diligence before deciding, in
2015, to embrace the cloud, company officials have said. "Capital
One is well-known among people that do cloud security for having
one of the strongest teams out there," Mr. Piper said.
The Capital One data breach isn't the first time data stored in
the cloud has been stolen. But the fact that the fifth-largest U.S.
credit-card issuer has become a victim is reviving concerns about
cloud computing. Capital One was an early adopter of cloud
computing and is featured as a case study on the AWS website.
The Federal Reserve, independent of the hack, has already been
scrutinizing the use of the cloud to store sensitive financial
records, the Journal has reported.
Ms. Thompson, in a posting from one of the accounts that
prosecutors said was hers, implied that she used such techniques to
target other companies' cloud-computing accounts, including Italian
bank UniCredit SpA and Ford Motor Co. Both companies have said they
are looking into it. The FBI has opened an investigation into the
other targets that it suspects Ms. Thompson might have hit.
Ms. Thompson's alleged actions may have gone unnoticed for far
longer if she hadn't bragged about them in an online forum.
Asa Fitch and Sebastian Herrera contributed to this article.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
August 04, 2019 05:44 ET (09:44 GMT)
Copyright (c) 2019 Dow Jones & Company, Inc.
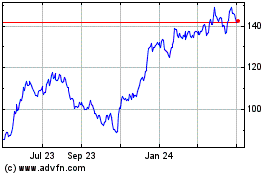
Capital One Financial (NYSE:COF)
Historical Stock Chart
From Jun 2024 to Jul 2024
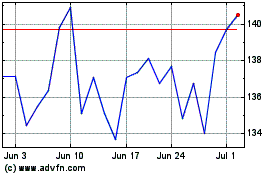
Capital One Financial (NYSE:COF)
Historical Stock Chart
From Jul 2023 to Jul 2024