TIDMNCC
NCC Group PLC
10 February 2023
NCC Group threat intelligence identifies ransomware attacks take
slight dip in 2022 as threat actors evolve and explore new
tactics
Highlights:
-- Ransomware attacks decrease 5% in 2022 (2,667 in 2021 to 2,531 in 2022)
-- Industrials sector was the most targeted by criminal gangs for second year running
-- North America (44%) and Europe (35%) most targeted regions
-- DDoS incidents and business email compromise (BEC) both take
a larger share of attack types as threat actors explore triple
extortion methods
-- Turbulence in threat landscape reflects wider grapple with
major conflicts and global economic uncertainty
Global cyber security and risk mitigation expert NCC Group
monitored a slight decrease of five per cent in ransomware attacks
in 2022 with 2,531 attacks, according to its 2022 Annual Threat
Monitor Report.
Although there were fewer attacks than in 2021, there was a
notable surge in ransomware attacks between February and April,
coinciding with the start of the Russia-Ukraine conflict when
prominent threat actor LockBit ramped up activity.
Analysis from across 2022 continues to highlight ransomware
operators as effective innovators willing to find any opportunity
and technique to extort money from their victims with data leaks
and DDoS being added to their arsenal to mask more sophisticated
attacks.
Compiled by NCC Group's Global Threat Intelligence team, the
report details the events of 2022 and their impact on the cyber
threat landscape, providing an overview of incidents across all
sectors and highlighting global trends.
The insights are based on incidents identified by NCC Group's
global managed detection and response service and its global Cyber
Incident Response team.
Sectors
The most targeted sectors in 2022 were Industrials* with 804
victim organisations (32%), followed by Consumer Cyclicals** with
487 (20%) and Technology*** with 263 (10%).
While this remains consistent with previous years, the report
called attention to a relative 10% surge in victim numbers for
'consumer cyclical' organisations - namely hotel and entertainment,
specialty retailers and homebuilding and construction supply
retailers - and financial services. Meanwhile, Software & IT
Services was the most targeted sector within Technology, which
presents multiple opportunities to threat actors, from the theft of
intellectual property to using victim companies for supply chain
compromises.
Regions
North America and Europe suffered the most ransomware attacks in
2022. North America bore the brunt, with 44% of all incidents
(1,106), a 24% decrease from 2021 (1,447).
Europe observed 35% of all incidents, with an 11% increase in
attack numbers, witnessing 896 in 2022 as compared to 810 in 2021.
It was potentially influenced by surges in activity associated with
the Russia-Ukraine conflict in the first half of the year.
Rise in DDoS and BEC attacks
The term 'ransomware' originally referred to a type of software
that encrypts data for the purposes of extortion. Then came double
extortion which covered ransomware and then a subsequent leaking of
sensitive data on a 'leak site'- also known as
'pay-now-or-get-breached'. Now prolific ransomware operators such
as Lockbit 3.0 are using DDoS attacks to add even more pressure to
a victim organisation - known as triple extortion.
NCC Group observed 230,519 DDoS events across 2022 with 45%
targeted at the United States, 27% of which occurred in
January.
This early surge in DDoS attacks and botnet-led breaches
reflects greater turbulence within the wider cyber threat
landscape, in part influenced by the Russia-Ukraine conflict. DDoS
continues to be weaponized by both criminal and hacktivist groups
as part of the conflict, alongside disinformation campaigns and
destructive malware, to cripple critical national infrastructure in
Ukraine and beyond.
Often garnering less attention than their ransomware
counterparts, business email compromise (BEC) attacks are clearly a
growing threat that organisations must pay attention to and
represented 33% of all incidents observed by NCC Group's Cyber
Incident Response team.
Matt Hull, NCC Group's Global Head of Threat Intelligence,
commented:
"2022 was another year that kept us on our toes. The threat
landscape has been heavily influenced by the conflict between
Russia and Ukraine, with a whole arsenal of offensive cyber
capabilities, from DDoS to malware, deployed by criminals,
hacktivists, and even other nations. Though perhaps not the
'cybergeddon' that some expected from the next big global conflict,
we are seeing state-sponsored attacks ramp up with cyber warfare
proving to be critical in this hybrid cyber-physical
battlefield.
"Despite this slight dip in ransomware attacks, this does not
mean we collectively declare 'job done'. Indeed, this decline in
attack volume and value is probably in part due to an increasingly
hard line, collaborative response from governments and law
enforcement, and of course the global impact of the war in Ukraine.
As a result, we have witnessed several coordinated operations in
2022 that saw arrests of key members of prolific cyber-criminal
operatives, as well as the disbanding of long established groups,
least of all Conti, which was 2021's most active group.
"In 2023, we expect bad actors to focus their attention on
compromising supply chains, bypassing multi factor authentication
(MFA) and taking advantage of misconfigured application programming
interfaces (API's). The threat will persist, and organisations must
remain vigilant, understand how they could be exposed and take
steps to mitigate any risk."
The full report is available for download from:
https://www.nccgroup.com/uk/annual-threat-monitor-report-2022/
Media contacts:
NCC Group Press Office
press@nccgroup.com
About NCC Group
NCC Group's purpose is to create a more secure digital
future.
As global experts in cyber security and risk mitigation, NCC
Group is trusted by over 14,000 clients to protect their most
critical assets from the ever-changing threat landscape.
Underpinned by insight, innovation, and intelligence, over 2,000
colleagues in North America, Europe, UK, and Asia Pacific help
organisations assess, develop, and manage their cyber resilience
posture.
This information is provided by Reach, the non-regulatory press
release distribution service of RNS, part of the London Stock
Exchange. Terms and conditions relating to the use and distribution
of this information may apply. For further information, please
contact rns@lseg.com or visit www.rns.com.
Reach is a non-regulatory news service. By using this service an
issuer is confirming that the information contained within this
announcement is of a non-regulatory nature. Reach announcements are
identified with an orange label and the word "Reach" in the source
column of the News Explorer pages of London Stock Exchange's
website so that they are distinguished from the RNS UK regulatory
service. Other vendors subscribing for Reach press releases may use
a different method to distinguish Reach announcements from UK
regulatory news.
RNS may use your IP address to confirm compliance with the terms
and conditions, to analyse how you engage with the information
contained in this communication, and to share such analysis on an
anonymised basis with others as part of our commercial services.
For further information about how RNS and the London Stock Exchange
use the personal data you provide us, please see our Privacy
Policy.
END
NRANKKBDKBKDPBD
(END) Dow Jones Newswires
February 10, 2023 05:16 ET (10:16 GMT)
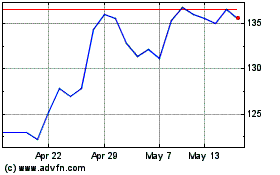
Ncc (LSE:NCC)
Historical Stock Chart
From Apr 2024 to May 2024
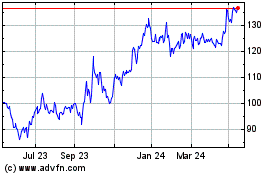
Ncc (LSE:NCC)
Historical Stock Chart
From May 2023 to May 2024