By Dustin Volz and Robert McMillan
A report concluding that Saudi Arabia likely hacked into Jeff
Bezos' smartphone has spurred questions and confusion among
cybersecurity experts, even as it has prompted renewed scrutiny of
the kingdom and its crown prince.
Cyberforensics specialists said the report, which is dated
November 2019 but didn't surface publicly until this week, relied
heavily on circumstantial evidence to make the case that a WhatsApp
account associated with Saudi Crown Prince Mohammed bin Salman was
probably used to hack into the iPhone of Mr. Bezos, the founder of
Amazon.com Inc. and owner of the Washington Post. They say the
audit left several major technical questions about the incident
unexplained and in need of more examination.
"It is not a conclusive report," said Bill Marczak, a researcher
with Citizen Lab, a Toronto-based technology watchdog that has
tracked Saudi Arabia's use of surveillance tools. "It raises some
interesting questions, some of which I think require further
explanation."
The report was produced by business-advisory firm FTI Consulting
following an investigation commissioned by Mr. Bezos. Gavin de
Becker, a security consultant hired separately by Mr. Bezos,
publicly alleged last March that the investigators had determined
"with high confidence" that the Saudis had accessed private
information on Mr. Bezos' phone.
The FTI report has already caused ripples, with two United
Nations officials on Wednesday publicizing its analysis and calling
on the U.S. to conduct further investigations, including into Saudi
Arabia's alleged use of commercial spyware to target political
opponents with intrusive digital surveillance.
FTI, which is based in Washington and has a presence in more
than two dozen countries, has repeatedly declined to comment
publicly about its study, citing client confidentiality. The report
said it had concluded -- with "medium to high confidence" -- that
the WhatsApp account associated with Prince Mohammed was used to
compromise Mr. Bezos' phone, likely by sending a video file in May
2018 that contained an image of the Saudi Arabian and Swedish flags
and an encrypted file.
Investigators said that video file appeared to contain malicious
code, citing as evidence that the phone began transmitting large
amounts of data hours after it was received.
Saudi Arabia has denied the allegations, calling them absurd.
Saudi officials close to the crown prince said they were aware of a
plan to hack Mr. Bezos' phone, but not of any attempt to blackmail
him, The Wall Street Journal reported on Wednesday.
A spokesman for Mr. Bezos declined to comment.
On Thursday, a White House spokesman said Saudi Arabia was an
"important ally" and declined to say whether the Trump
administration planned to investigate the matter.
The FTI investigation appeared to forgo important investigatory
steps that could have yielded a fuller picture of what occurred on
Mr. Bezos' iPhone X, forensics specialists said.
Perhaps the most important piece of evidence absent from the
report, experts say, is the malicious software allegedly used to
hack into Mr. Bezos' phone. The FTI report suggests this so-called
malware may lie in an encrypted file sent to Mr. Bezos' phone, but
FTI said it wasn't able to decrypt this file.
That is something it should be able to do, according to both Mr.
Marczak and Alex Stamos, director of the Stanford Internet
Observatory at Stanford University, who until August 2018 was chief
security officer at Facebook Inc., which owns WhatsApp.
According to Mr. Stamos, the report suggests that FTI
investigators had access to the data necessary to decrypt the file
in question and examine it for malicious software. "They don't seem
to understand how to properly decrypt WhatsApp attachments," Mr.
Stamos said.
In its report, FTI said it received Mr. Bezos' iPhone X in May
2019 and began efforts to try to collect evidence, keeping the
device in a lab secured and staffed 24 hours a day, with no other
electronic devices allowed in or out. The report didn't say whether
the phone was prohibited from connecting to the network.
The FTI report indicates that the firm didn't perform a
"jailbreak" of the phone -- a way of circumventing the security
restrictions that hamper the viewing of files on the phone. A
jailbreak is an important step in many forensics investigations,
particularly those searching for sophisticated hacking software,
Mr. Stamos said. "If your goal is to determine if there is
nation-state-level malware on a device, you can't do that without a
jailbreak," he said.
A person familiar with the investigation acknowledged that a
jailbreak of the iPhone would likely be necessary to obtain more
definitive results, and that FTI investigators still wanted to do
that, as the report's final page states. But there were
circumstances that have delayed that effort, this person said,
while declining to provide specifics.
The report indicates that the investigation may have been
hampered by a common security issue: password problems.
Investigators wrote that they lacked the password for the iTunes
backup for Mr. Bezos' phone -- the report didn't explain why Mr.
Bezos couldn't provide it -- and that in May they bypassed the
phone's backup encryption password to create a copy of the phone's
files. That is a common investigative technique when the backup
password is missing, but it reduces the amount of phone data
available to investigators, said Sherri Davidoff, the chief
executive of LMG Security, a Missoula, Mont.-based cybersecurity
company that conducts forensic investigations.
The FTI review also didn't explain whether Mr. Bezos was duped
into clicking on a malicious file, or if malware had been
automatically installed on his device -- a rare but powerful
hacking technique.
Experts said the massive surge in outgoing data that began hours
after Mr. Bezos received the file could signal malicious activity.
While the timing of the surge was suspicious, experts said it was
circumstantial evidence that alone isn't sufficient to conclude
that a hack took place.
FTI isn't among the firms best known for cyberforensics
investigations. Founded 38 years ago, it advises companies across
the globe on a range of sensitive matters, including corporate
litigation and forensic accounting. It has been involved in several
other prominent cases, including the Enron and WorldCom
bankruptcies and the investigation into the use of steroids in
Major League Baseball.
The company has sought to expand its cybersecurity portfolio
rapidly in recent years, and in 2017 hired Anthony Ferrante as its
global head of cybersecurity. Mr. Ferrante, a veteran of the
Federal Bureau of Investigation who was chief of staff of the
agency's cyber division, served as director for cyber incident
response at the National Security Council during the Obama
administration. Mr. Ferrante was the author of the report on Mr.
Bezos' phone.
FTI maintains close ties to law enforcement, recruiting heavily
from the FBI and U.S. intelligence agencies, and Mr. Ferrante has
been involved in other high-profile investigations.
Several former U.S. cybersecurity officials who have worked with
Mr. Ferrante described him as a straightforward investigator with
real technical skills. "Anthony is a professional," said one former
colleague. "He is not the kind of person who puts something out
without real confidence."
Mr. Ferrante declined to comment.
Write to Dustin Volz at dustin.volz@wsj.com and Robert McMillan
at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
January 24, 2020 06:44 ET (11:44 GMT)
Copyright (c) 2020 Dow Jones & Company, Inc.
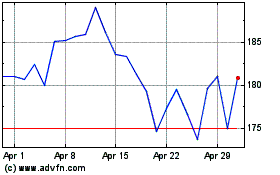
Amazon.com (NASDAQ:AMZN)
Historical Stock Chart
From Apr 2024 to May 2024
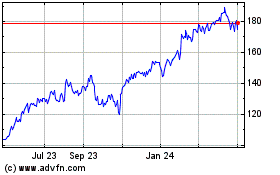
Amazon.com (NASDAQ:AMZN)
Historical Stock Chart
From May 2023 to May 2024